I promise this is not yet another tutorial on how to publish a static website using AWS S3, or at least not solely smashing the S3 content onto the web. I’d like to show you a GitHub project that uses Java to orchestrate Cloudformation when deploying the architecture of a static website.
The main purpose of this tool is going beyond the S3 out of the box website functionality, that is:
- Make the S3 bucket private (so, secure)
- Provide HTTPS certificates (secure, again)
- Serve the content via cloudfront cache (so, fast)
- Hide the complexities of working with Cloudformation
I’m in for fast and secure, but free…ish?
Not all the resources that need to be fired up for this architecture are within the AWS free tier, expecially the domain. Nevertheless, all the costs that I’ve seen after this website was published were only live costs. Let’s review them from the most to the least expensive:
- The domain: 20€ / year if hosted on Route53 (as marcoaguzzi.it) but you can host it elsewere (on cloudns, and it’s free)
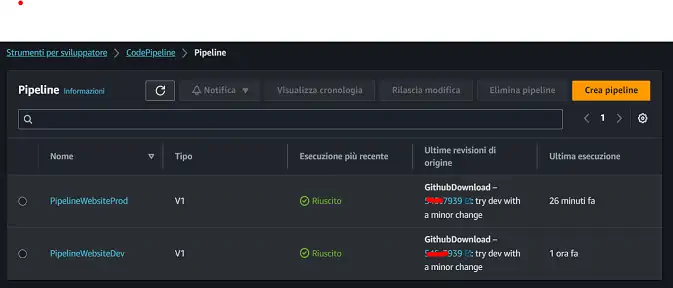
- Route53 and Codepipeline: 1€ / month each. It’s one for the hosted zone and one for the pipeline. The pipeline comes with a good amount of free build / minutes
- Secret manager: less than 0.5€ / month (there’s a grace period when started)
- Cloudfront and S3: 0.01€ / month each
Of course these are starting costs, they can go a lot higher as the usage increase, but it should be a welcomed issue, I suppose
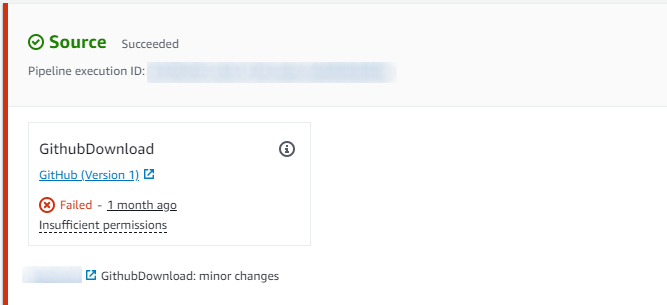
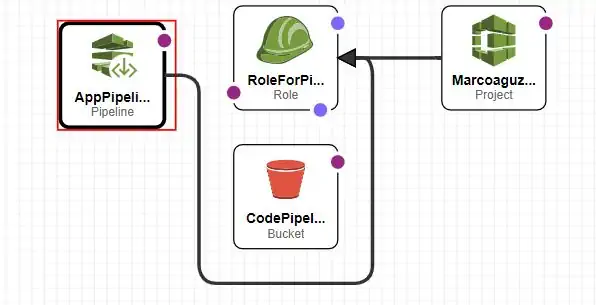
Cloudformation migth be a burden to use, especially within the web UI. These are the main issue I addressed in the project:
- Have a self - contained architecture
- Be repeatable. Could it deploy the same architecture on another domain?
- Ease the deploy process, especially when the domain is not hosted on Route53
- The nested stacks are not automatically resolved by Cloudformation
While experimenting with Java and Gradle, I wondered if I could use Java to mitigate the problems listed above by orchestrating the instructions that Cloudformation needs in order to deploy the website. This turned out as a Github project: https://github.com/maguzzi/s3_static_website_gradle. The Gradle build creates a distributable archive with all the needed jars.
![Please stop publishing AWS S3 buckets as static websites! Read here for a secure, fast, and free-ish approach [1st episode]](/img/tool-for-static-website/banner.png)


![Please stop publishing AWS S3 buckets as static websites! Read here for a secure, fast, and free-ish approach [1st episode]](/img/tool-for-static-website/banner_thumb.png)


